Intro - Parallels to the Cocoa Fair Trade Concept
Across the world, a bar of chocolate begins its journey on small tropical farms. For many cocoa growers, the value of their harvest is determined far away within complex global supply chains. To address this imbalance, Fairtrade International created a certification system that increases transparency and accountability, helping farmers receive a fairer share of the value their crops generate.
A similar imbalance appears in the global meteorite trade. The first people to recover these fragments, often local finders in remote landscapes, usually receive only a small fraction of their eventual value. As meteorites pass through networks of traders, dealers, and collectors, their origins can become uncertain and the finders have little bargaining power.

In the cocoa sector, certification relies on traceable origin, cooperative organization, and minimum pricing to rebalance the system. A comparable approach could exist for meteorites regarding the traceability of their origin. Authenticated geolocation and reliable provenance records could trace meteorites to the landscapes where they landed, bringing transparency to the market.
Meteorites are part of the nation’s scientific and natural heritage. When specimens are removed without proper documentation, their discovery locations can disappear from the scientific record. Establishing reliable geolocation therefore supports fairer trade while preserving the scientific and cultural value of these visitors from space.
Context and Challenge
Across deserts, ice fields, and remote plains, meteorite hunters search for fragments of worlds beyond Earth. Yet the moment a meteorite is found, a surprisingly terrestrial problem arises: where exactly was it discovered?
In meteorite science and law, location is everything. The geographic coordinates of a find are the legal trigger for nearly all regulatory and scientific processes. They determine jurisdiction, ownership claims, export permissions, and the scientific value of the specimen itself. Without precise and verifiable coordinates, enforcement agencies cannot confirm whether a meteorite was recovered legally, nor can scientists reliably place the object within its geological and environmental context.
A meteorite stripped of its location is, in many ways, stripped of its story.
Today, much of this information relies on handwritten notes, unverified GPS readings, or informal documentation. While many meteorite hunters maintain careful records, the system remains vulnerable to error, loss, and fraud. As meteorite collecting grows in scale and commercial value, the need for trusted geolocation and verifiable documentation has become increasingly clear.
A Technological Opportunity
A potential solution may already be orbiting above us.
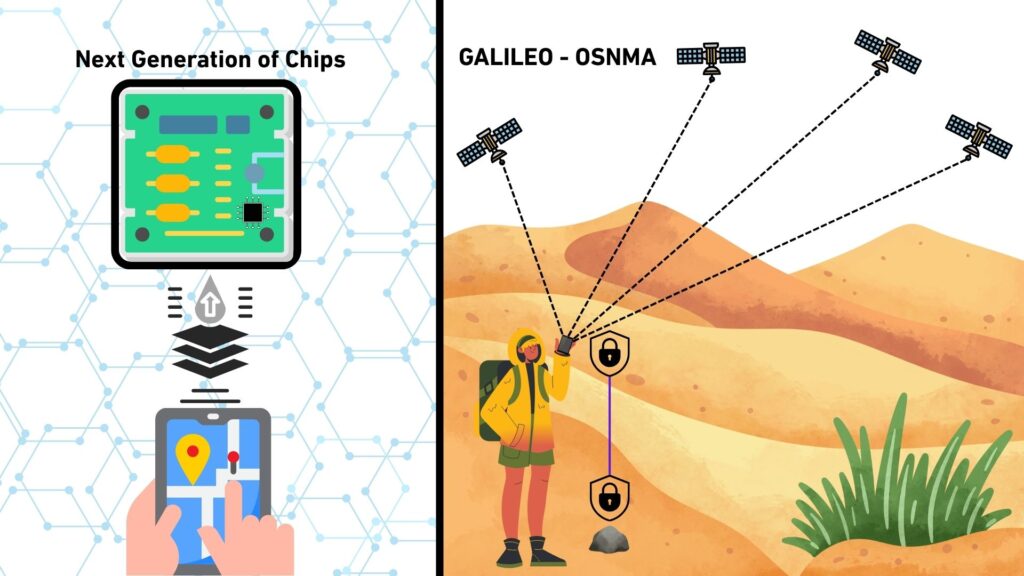
The European Union’s Galileo Satellite Navigation System has recently introduced a capability known as Open Service Navigation Message Authentication (OSNMA). Unlike conventional satellite navigation signals, which can be spoofed or manipulated, OSNMA provides cryptographic authentication of navigation messages. In simple terms, it allows receivers to confirm that the satellite signal, and therefore the position derived from it, is genuine.
New generations of GNSS receiver chips are beginning to support OSNMA, enabling authenticated positioning directly within consumer devices. As this technology matures, it is expected to become available in everyday electronics, including smartphones.
This development opens an intriguing possibility: verifiable geolocation at the moment of discovery.
A Possible Application
Imagine a dedicated meteorite-hunting application built around authenticated satellite positioning. Such a system could transform how meteorite discoveries are documented. The app could be built to handle all the aspects below.
Verified User Registration
Participation would begin with registration. Users would identify themselves as meteorite hunters and undergo a basic identity verification process. This step would help prevent fraudulent reporting while ensuring traceability of discoveries.
Authenticated Location Capture
When a meteorite is discovered, the application would access the smartphone’s GNSS receiver and obtain coordinates authenticated through OSNMA. The resulting location would not merely be recorded; it would be cryptographically verified as genuine satellite-derived data.
Structured Documentation of the Find
To document the discovery, the application could require the user to capture a set of high quality photographs, perhaps ten or more, showing both the meteorite and the surrounding site from multiple angles.
Each image would contain encrypted metadata embedding a precise timestamp, authenticated GNSS coordinates, a device identity signature, and magnetic orientation data derived from the phone’s sensors, allowing the original orientation of the meteorite relative to Earth’s magnetic field to be reconstructed.
In effect, every photograph would become a small, tamper resistant scientific record.
A Gateway to Registration and Export
Submission through such an application could become a prerequisite for official meteorite registration or export permits. The result would be a standardized digital record linking the specimen, the finder, and the precise place and moment of discovery.
Meteorite recovery has long been driven by passionate individuals exploring remote landscapes in search of outer space visitors. Yet the documentation of these discoveries has not kept pace with modern technology.
An authenticated digital workflow could change that.
By combining satellite authentication, secure metadata, and ubiquitous smartphones, meteorite discoveries could be recorded with a level of rigor previously reserved for professional scientific expeditions. The result would not replace the thrill of the hunt. Rather, it would ensure that when a meteorite fragment is lifted from the ground, its story, from the moment of discovery onward, is preserved with scientific certainty.
In doing so, meteorite hunting could evolve from a loosely documented activity into a globally traceable, digitally verifiable scientific process powered by tools already in our pockets.

Can Galileo-OSNMA disrupt how meteorite finds are documented?
Speaking from a purely technical perspective and acknowledging that legal frameworks differ widely from country to country, the ability to obtain an authenticated geolocation for a meteorite discovery is now within reach. Within the next two to three years, this capability is likely to become available to virtually every smartphone user. What has long been a conceptual solution to the problem of verifiable discovery locations is now becoming a practical technological reality.
The enabling technology comes from the European Union’s global navigation infrastructure, the Galileo Satellite Navigation System, and specifically from its recently introduced functionality known as Open Service Navigation Message Authentication (OSNMA). This authentication capability was officially commissioned in July 2025 and represents a significant advance in the reliability and security of satellite based positioning.
To understand why this matters for meteorite discovery, it is useful to briefly consider how the Galileo system determines position.
Under-the-hood view of Galileo and the OSNMA functionality
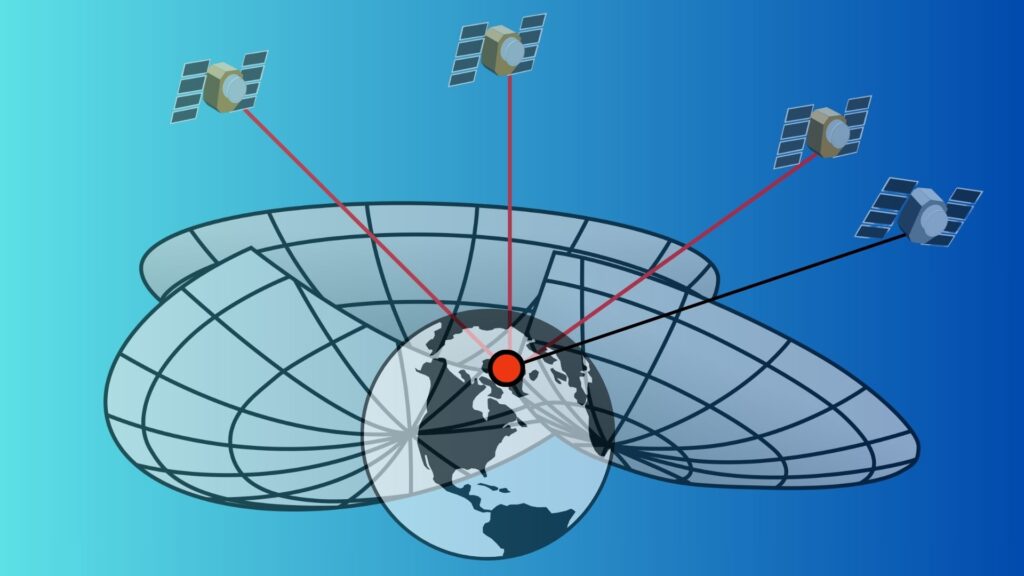
Galileo is Europe’s global satellite navigation system, developed by the European Union and operated by the European Union Agency for the Space Programme. A constellation of satellites orbiting Earth continuously broadcasts radio signals that contain very precise time information together with navigation data describing the satellite’s position in space.
A receiver on the ground, such as the one built into a smartphone, listens to signals from several satellites at once. By comparing the time a signal was transmitted with the time it was received, the device can calculate how far away each satellite is. Because radio signals travel at the speed of light, even tiny differences in timing translate into measurable distances.
To determine its exact position on Earth, the receiver must obtain signals from at least four satellites. Using these distance measurements together with information about the satellites’ positions contained in the navigation message, the device performs a geometric calculation known as trilateration. In simple terms, each measured distance defines a sphere around a satellite, and the receiver’s location is the point where several of these spheres intersect. The fourth satellite measurement allows the receiver to correct the small error in its internal clock while simultaneously solving for latitude, longitude, and altitude.
The Navigation Message
The navigation message is a digital data stream transmitted by each satellite together with the timing signal. It provides the information the receiver needs to interpret the signal and compute its position. This includes data describing the satellite’s orbit, corrections for small variations in the satellite’s atomic clock, system time information, and the operational status of the satellite.
When a receiver collects signals from multiple satellites, it uses the navigation message to determine where each satellite was located at the moment the signal was transmitted. Combined with the measured signal travel time, which provides the distance to each satellite, the receiver can determine its position on Earth.
Navigation Message Authentication (OSNMA)
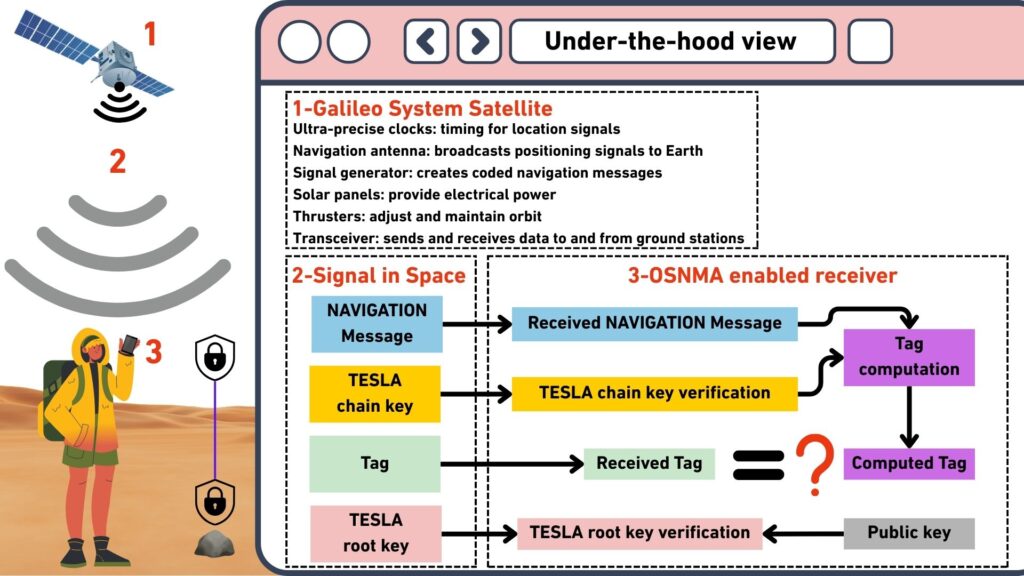
Traditional satellite navigation signals can be imitated by malicious transmitters, a technique known as spoofing. In such an attack, false signals are broadcast in order to mislead receivers about their true location. To address this vulnerability, the Galileo system provides an authentication mechanism called Open Service Navigation Message Authentication.
The purpose of OSNMA is to allow receivers to verify that the navigation message they receive truly originates from Galileo satellites and has not been manipulated. This is achieved by adding cryptographic authentication data to the navigation message itself.
The process begins within the Galileo ground infrastructure, where cryptographic keys are generated and managed. Using these keys, authentication codes are created for parts of the navigation message. These codes function as digital signatures that prove the authenticity of the transmitted data. The authentication information is then uploaded to the satellites together with the navigation data.
As the satellites broadcast their signals, they transmit the navigation message along with short cryptographic codes known as authentication tags. These tags are mathematically linked to the navigation data and allow a receiver to verify its authenticity at a later moment. However, the receiver cannot immediately verify the tag because the cryptographic key required to check it has not yet been disclosed.
The system therefore uses a security method known as TESLA, which stands for Timed Efficient Stream Loss tolerant Authentication. In this approach, authentication tags are transmitted first, while the cryptographic key used to generate them is broadcast only after a short delay. During this period the receiver stores the navigation message together with the received authentication tags.
After the delay, the satellite transmits the cryptographic key that was used to generate the earlier authentication tags. Once the receiver receives this key, it can recompute the authentication codes and compare them with the tags it previously stored. If the values match, the receiver confirms that the navigation message was generated by the authentic Galileo system and that the data were not modified during transmission.
Once this verification step succeeds, the receiver can safely use the authenticated navigation data for positioning. If the authentication check fails, the receiver can reject the suspicious signal and warn that the navigation data may have been spoofed.
For applications that depend on trusted geolocation, such as the authenticated documentation of meteorite discoveries discussed earlier, this capability is particularly significant. By cryptographically verifying the origin and integrity of the navigation message, OSNMA allows receivers to confirm that their computed position truly corresponds to signals broadcast by the Galileo satellite constellation. In practical terms, this transforms satellite positioning from a system based largely on trust into one where the authenticity of the location itself can be verified.
Why a New Generation of Chips Was Needed?
The introduction of Open Service Navigation Message Authentication (OSNMA) within the Galileo Satellite Navigation System required a new generation of GNSS receiver chips. Earlier positioning chips were designed mainly to receive satellite signals, decode navigation data, and compute a geographic position. They were not built to verify whether those signals were authentic.
OSNMA adds a cryptographic layer that allows receivers to confirm that navigation messages truly originate from Galileo satellites and have not been manipulated. To perform this verification, receivers must be able to process authentication codes, temporarily store navigation data, and validate it once the corresponding cryptographic key is broadcast. These tasks require additional computing capability and secure memory inside the receiver, which older GNSS chips generally do not provide.
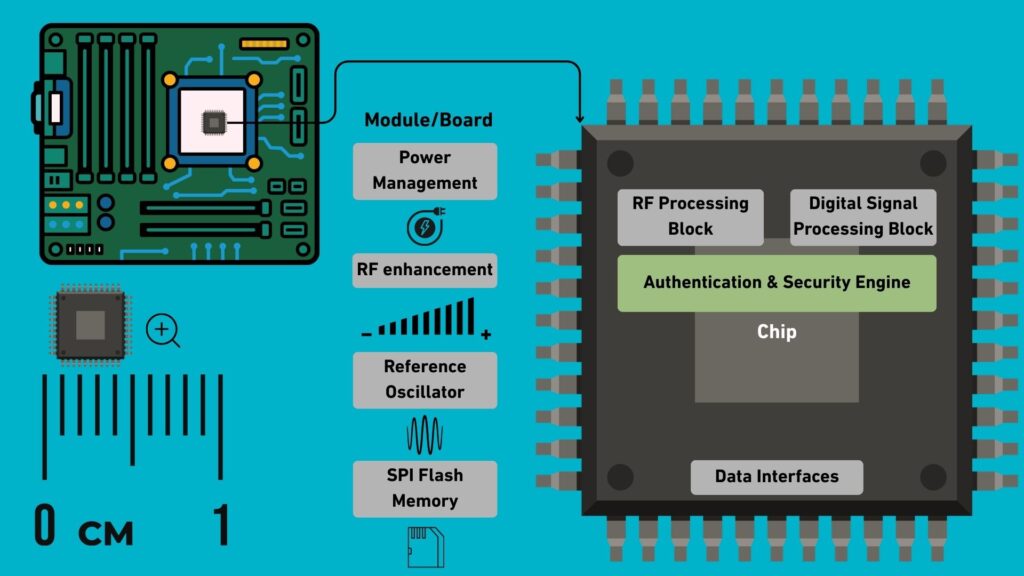
Modern OSNMA capable chips therefore include cryptographic processing functions and protected memory for authentication data. They can also indicate whether the navigation data used to compute a position has been successfully authenticated. This allows applications to distinguish between ordinary positioning data and verified satellite signals.
Importantly, these chips remain compatible with existing satellite navigation services. They can function like traditional GNSS receivers when authentication is unavailable, while enabling verified positioning when OSNMA signals are present.
As new GNSS chipsets are adopted by smartphone manufacturers, this capability is expected to spread gradually through the consumer market, first appearing in high end devices and later becoming common across mainstream smartphones. In the near future, authenticated satellite positioning may therefore become a standard feature available to everyday users.
Legal Framework
Meteorites are governed by terrestrial law, not space law. This means their ownership depends entirely on the country where they are found. Different nations apply very different legal approaches. Some grant ownership to landowners, others to the state, and some classify meteorites as protected cultural or scientific heritage. In countries such as Morocco, Algeria, and Oman, meteorites may fall under national heritage protections or state control.
In this context, precise geolocation becomes critical. Verified find coordinates determine which national law applies, whether export permits are required, and whether ownership belongs to a private finder or the state. Without authenticated coordinates, enforcement becomes extremely difficult. Export controls weaken, provenance disputes multiply, and authorities cannot verify compliance. In practical terms, geolocation is the legal trigger that allows regulation to function.
The Approach of the Meteorite Society
To bring order to the scientific record, the Meteoritical Society requires that newly classified meteorites be accompanied by basic geographic information before they are listed in the Meteoritical Bulletin Database. Submissions typically include a documented find location, geographic coordinates when possible, and a geographic name linked to the nearest landscape feature.
This information anchors meteorites to a specific place on Earth. For planetary scientists, that geographic context helps reconstruct fall events and interpret the geological setting of a discovery.
When the Exact Location Is Unknown
In many desert regions, meteorites are recovered through informal searches where precise locations are not recorded. To allow these specimens to still be studied, the Nomenclature Committee assigns broad regional names. One of the most common designations is “Northwest Africa,” often abbreviated as NWA.
Under this system, meteorites from countries such as Morocco, Mauritania or Mali may receive sequential identifiers such as NWA 869, NWA 7034, or NWA 12264. The numbering reflects the order of approval rather than geographic proximity.
Scientific Consequences
This system allows classification, but it comes with scientific costs. Without precise find locations, provenance remains ambiguous. Researchers struggle to determine whether fragments belong to the same fall, known as pairing. Reconstructing a strewnfield, the pattern created when a meteorite breaks apart in the atmosphere, becomes nearly impossible. The surrounding geological context is also lost.
Even so, the NWA designation remains an important compromise. It allows scientifically valuable meteorites to enter the formal record and become available for research, even when their exact recovery locations are unknown.
The pathway of a meteorite discovered in Africa
In the global meteorite market, two very different pathways exist. The difference between them is not the rock itself, but the moment at which its origin is documented. If authenticated geolocation is used from the outset, the first pathway becomes possible, creating a transparent and legally robust chain that preserves both scientific and economic value.
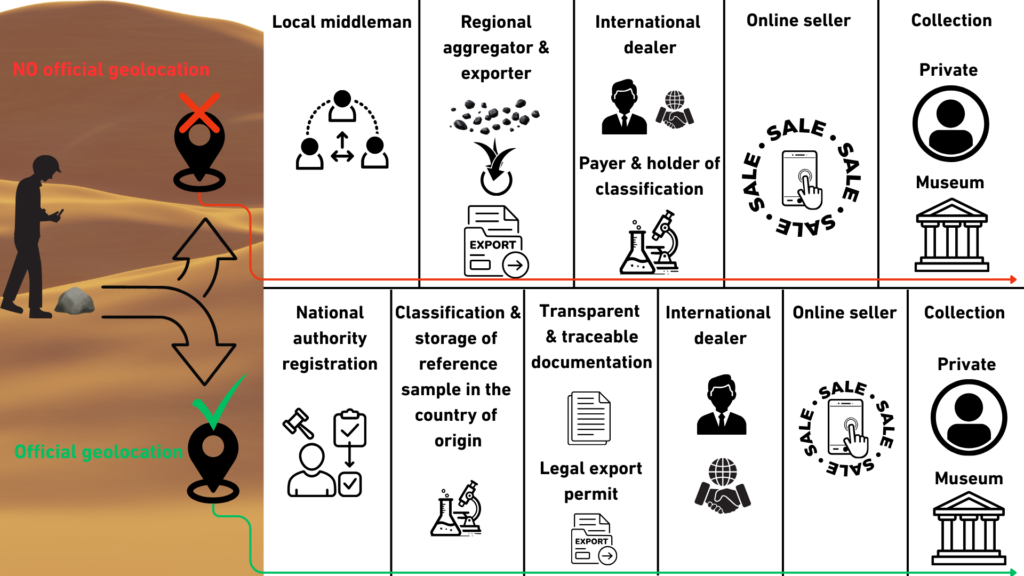
The first pathway describes fully documented meteorites. The process begins when the finder records exact coordinates and documents the discovery with photographs and contextual notes. Where required, local authorities or landowners confirm legal ownership and authorize recovery. A small sample is then submitted for scientific classification, and the discovery is formally registered with the Meteoritical Society for inclusion in the Meteoritical Bulletin Database. Once classified and named, the specimen may pass through licensed exporters, international dealers, and auction houses, each step supported by documentation that links the meteorite to its recorded coordinates. In this model, authenticated geolocation anchors the entire chain, enabling legal compliance, scientific traceability, and clear provenance. Value increases at stages such as classification, certification, and formal sale, while transparency remains intact.
The second pathway dominates in regions where authenticated geolocation is not recorded. In parts of Morocco, Algeria, Western Sahara meteorites are often discovered without GPS documentation and quickly enter informal trade networks. Stones may move from local finders to middlemen, then to regional aggregators and export brokers, frequently in bulk lots where individual origins are no longer distinguishable. When samples are later submitted for classification, they are commonly assigned generic designations such as “Northwest Africa” with sequential numbers. Although this system allows scientific classification, the absence of precise coordinates means that pairing studies, strewnfield reconstruction, and full geological context are often impossible. In this pathway, documentation is fragmented early, export legality may be unclear, and scientific provenance is permanently weakened.
When authenticated geolocation is applied consistently, the first pathway can become the standard model. Coordinates recorded at the moment of discovery transform the meteorite from an anonymous object into a traceable scientific specimen, aligning legal clarity, fair trade, and preservation of planetary heritage within a single transparent system.
Note on Scope
This article discusses and focuses primarily on the technical opportunities enabled by Galileo OSNMA, particularly in relation to authenticated geolocation and its potential application to meteorite discovery. It examines how advancements in GNSS authentication could support more reliable and tamper-resistant documentation of find locations. However, it also acknowledges that this perspective is limited in scope and does not fully address the many legal, regulatory, and practical complexities involved in real-world implementation. In particular, aspects such as national meteorite ownership laws, variations in export regulations, and the dynamics of the global meteorite trade are only briefly considered, and require deeper interdisciplinary analysis beyond the technical focus of this article.
References
[1] – Borre, D. M. Akos, N. Bertelsen, P. Rinder, and S. H. Jensen, “A software-defined GPS and Galileo receiver: A single-frequency approach,”Birkhäuser, 2007.
- This work provides a comprehensive introduction to GNSS fundamentals, including signal structure, satellite geometry, and navigation message decoding. It explains how GNSS receivers process signals from satellites to determine position, velocity, and time, with a strong focus on practical implementation using software-defined radio techniques.
[2] – European Union, “Galileo Open Service Signal-In-Space Interface Control Document (OS SIS ICD),” Issue 2.1, European GNSS Service Centre (GSC), 2021. [Online]. Available: https://www.gsc-europa.eu
- This document elaborates on the structure, content, and technical specifications of the Galileo Open Service signals transmitted by the satellite constellation. It defines how navigation data is formatted and broadcast, including timing information, satellite orbit parameters, and signal characteristics required for positioning. The document also specifies interface requirements for receiver design, enabling manufacturers and developers to correctly interpret the signals and ensure compatibility with the Galileo Open Service.
[3] – European Union, “Galileo Open Service Navigation Message Authentication (OSNMA) Signal-In-Space Interface Control Document (SIS ICD),” Issue 1.1, European Union Agency for the Space Programme (EUSPA), Oct. 2023. [Online]. Available: https://www.gsc-europa.eu/sites/default/files/sites/all/files/Galileo_OSNMA_SIS_ICD_v1.1.pdf
[4] – Trex2001, “GPS Spherical Location,” Wikimedia Commons, 2010. [Online]. Available: https://commons.wikimedia.org/wiki/File:GPS_Spheres.svg, licensed under CC BY-SA 3.0 (https://creativecommons.org/licenses/by-sa/3.0/). Changes were made. This work is distributed under the same or a compatible license.
[5] – M. Gounelle, “Meteorites: International law and regulations,” Meteoritics & Planetary Science, vol. 54, no. 12, pp. 2887–2901, 2019.
- This paper provides a comprehensive overview of the legal status of meteorites across different legal systems, including international law, national law, and transnational scientific regulation. It examines how meteorites are treated simultaneously as scientific objects, commercial goods, and cultural heritage items, leading to complex and sometimes conflicting legal interpretations.
[6] – D. G. Schmitt, “The law of ownership and control of meteorites,” Meteoritics & Planetary Science, vol. 37, suppl., pp. B5–B11, 2002. Available: https://www.lpi.usra.edu/meetings/metsoc2001/pdf/5150.pdf
- This paper analyzes ownership laws and regulatory approaches for meteorites across different countries, focusing on how increasing commercial interest in meteorites raises legal and ethical challenges. It compares legal systems and examines how laws affect scientific access, trade, and reporting of meteorite finds.
[7] – Fernández-Hernández, Ignacio, Gonzalo Seco-Granados, and José Antonio López-Salcedo. 2021. “Computational Load Analysis of a Galileo OSNMA-Ready Receiver for ARM-Based Embedded Platforms.” Sensors 21 (2): 467. https://doi.org/10.3390/s21020467.
- This paper analyzes the computational and architectural requirements of implementing Galileo Open Service Navigation Message Authentication (OSNMA) in GNSS receivers, with a focus on ARM-based embedded platforms. It demonstrates how authentication introduces additional processing, memory, and system design demands, highlighting the modifications needed for receivers to securely verify satellite navigation data.